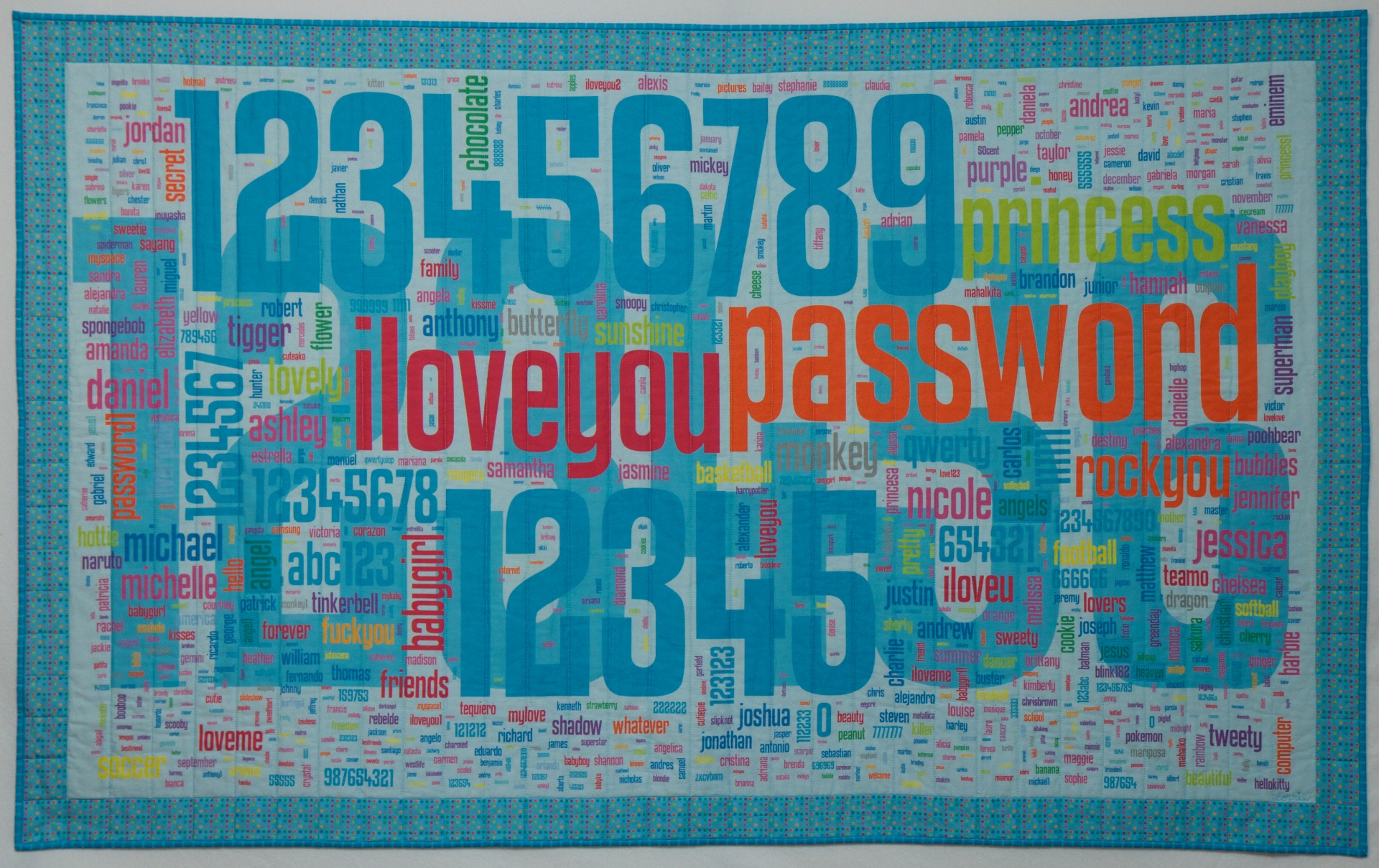
Lorrie Faith Cranor studied thousands of real passwords to figure out the surprising, very common mistakes that users — and secured sites — make to…
Tag: passwords
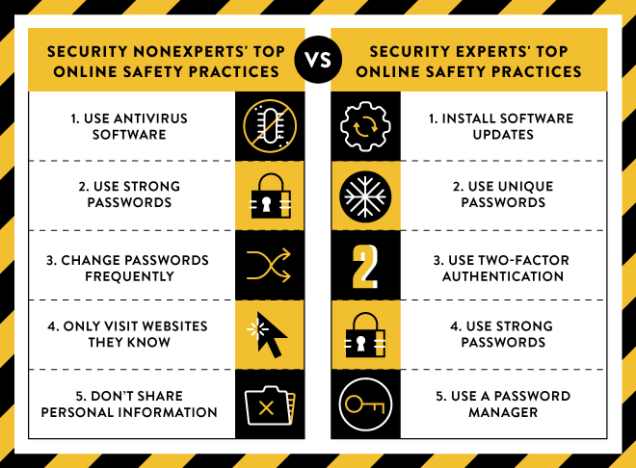
If you ask the average person what the best ways to protect themselves online are, they’ll give some true answers—but they’ll likely be different than…
Ian Urbina, author of The Secret Lives of Passwords, talks about what passwords mean to people beyond their access to email or social networking accounts.…
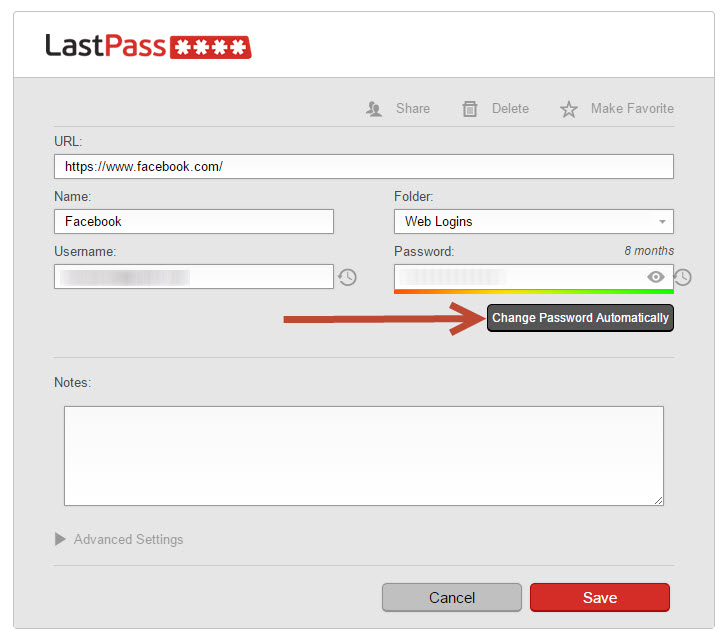
Here’s the video of my LastPass presentation from the Nebraska Library Association Conference presented on 10 October 2014.
In case you needed yet another reason to use LastPass… We’re excited to announce that the Auto-Password Change feature we released to our Pre-Build Team…
Bravo WordPress! This week, a group of hackers released a list of about 5 million Gmail addresses and passwords. This list was not generated as…
Ebay says that its corporate network and databases were compromised earlier this year, and will ask its users to change their passwords. Read more @…
Published on Apr 13, 2014 Leo demonstrates how to create and use secure passwords with LastPass.
I’ve been putting off this post for a few days to allow for the immediate freak-out to die down and to let some actually good…