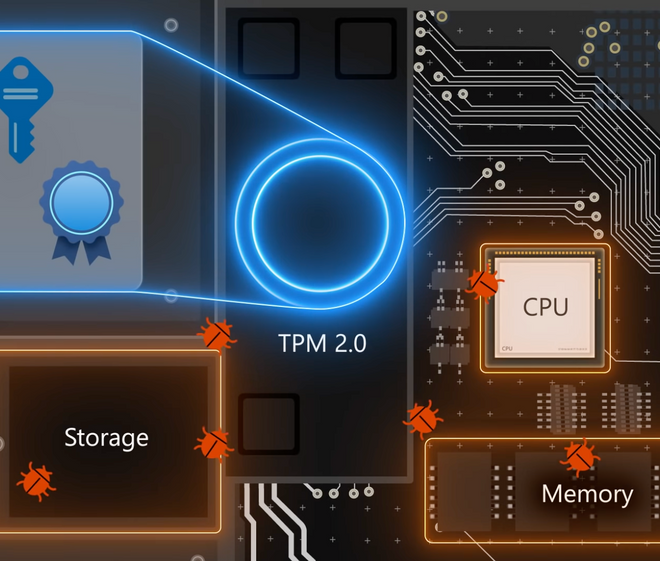
Stay ahead of external and internal threats — and balance performance, reliability, and security with Windows 11. Dave Weston, Windows security expert, joins Jeremy Chapman…
Tag: microsoft
Explore a speculative digital world without screens in this fanciful demo, a mix of near reality and far-future possibility. Wearing the HoloLens headset, Alex Kipman…
Wondering about how the Windows 10 upgrade is going to work, how much it’s going to cost, or if your existing hardware will work? Microsoft…
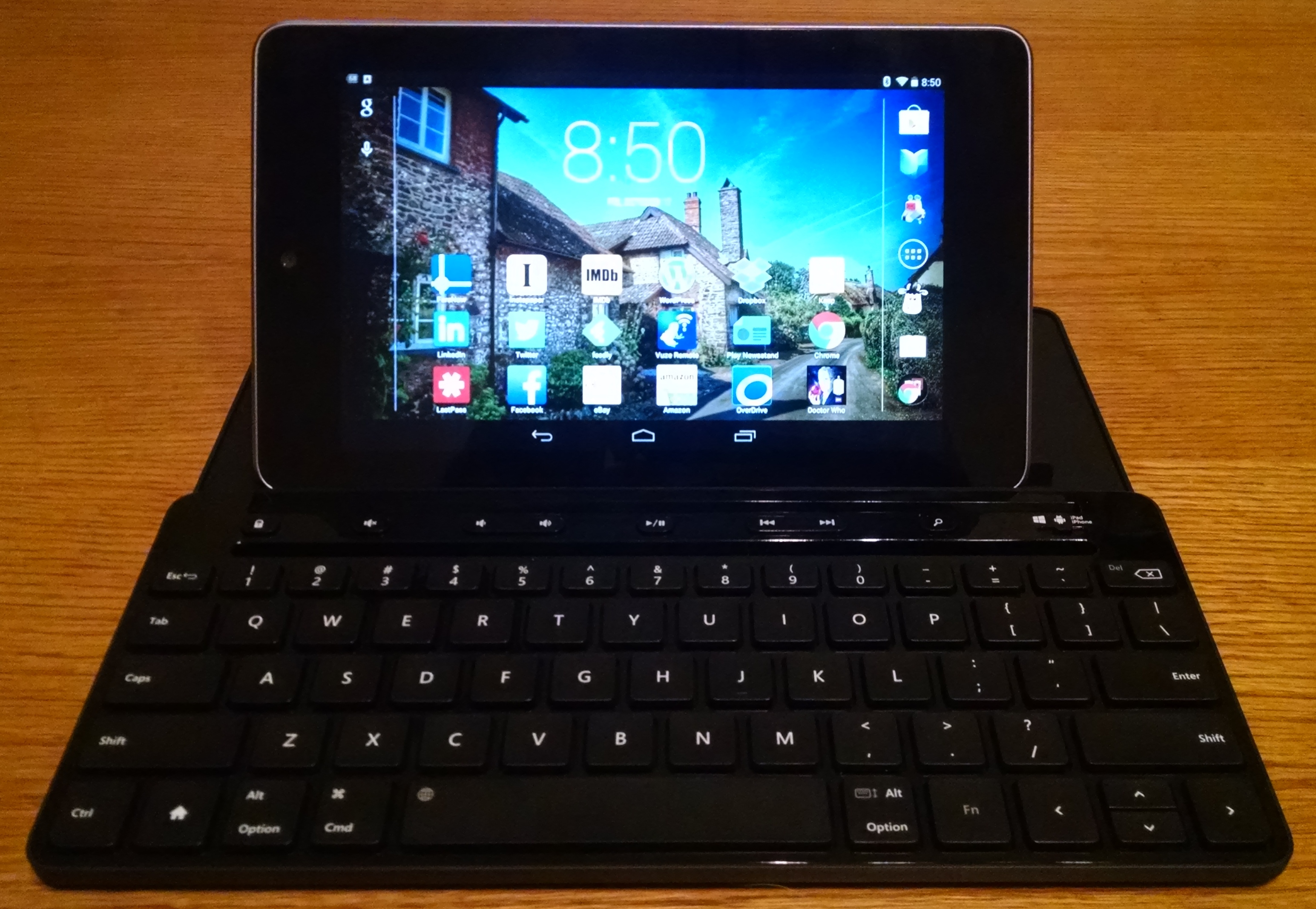
My lovely wife got me a keyboard for my birthday: The Microsoft Universal Mobile Keyboard. It’s bluetooth and works with Android, iOS and Windows. It’s…
In my Windows 10 presentation yesterday a question was asked about the Windows 10 Technical Preview having a keylogger. I said it did and that…
The first technical preview of Windows 10 (yes, they’re skipping Windows 9) has been released and Michael has been testing it. Join us for a…
Have a spare machine you can use to test Windows 10? If so, you can head on over to http://preview.windows.com and sign up for the…
Two videos this week. The first is the very short intro to Windows 10 and the second is the full live presentation from September 30th.