Imagine that you wanted to train a facial recognition algorithm on age-related characteristics and, more specifically, on age progression (e.g., how people are likely to…
Tag: privacy
Phil Zimmermann, the creator of PGP and Silent Phone is our guest at Google, talking about communications security. How large scale deployments of end-to-end secure…
There are very few government checks on what America’s sweeping surveillance programs are capable of doing. John Oliver sits down with Edward Snowden to discuss…
Here’s the video of my LastPass presentation from the Nebraska Library Association Conference presented on 10 October 2014.
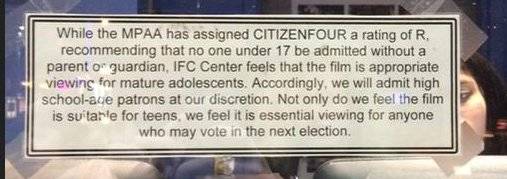
I saw Citizenfour last weekend and I’m at a loss as to why this film was rated R. At least one theatre felt the same…
The ALA published a report investigating the use of filters and found they were disproportionately blocking out left-leaning views on issues such as gay marriage…
Harvard Law School Professor Lawrence Lessig interviewed Edward Snowden at Harvard Law School on Oct. 20.
Adobe came under fire a few weeks ago when news was brought to light that critical user data was being sent to their servers from…
This is from May but I’m a bit behind in some of my reading. However it is worth every moment you’ll spend reading it. A…